Most small business owners in Lincoln and Omaha believe they are flying under the radar. You think your business is too small to be a target. You think because you have a firewall and a basic antivirus, you're "good."
The truth is uncomfortable. Hackers aren't just looking for the giants. They are looking for the path of least resistance. In Nebraska, that path usually leads straight through the very tools you use to run your business every day. Your email, your remote access, and even your security cameras are often the biggest vulnerabilities in your building.
If you’re tired of the "set it and forget it" IT mentality that leaves your back door wide open, it’s time to see what’s actually happening behind the screen.
The Tools You Trust Are the Tools They Use
Hackers love your IT tools. Why? Because you trust them. If a hacker can compromise a tool your staff uses daily, they don’t have to "break in", they just walk through the front door with a valid key.
In many small businesses across Omaha and Lincoln, IT tools are installed, configured with default settings, and then ignored until something breaks. This is exactly what cybercriminals count on. They aren't looking for a "super-virus"; they are looking for a misconfigured Microsoft 365 account or an unpatched VPN.
Microsoft 365 and Google Workspace: The Unlocked Front Door
Most businesses use these platforms for everything. If a hacker gets into one employee's email, they have access to your invoices, your client lists, and your internal communications. They don't immediately steal your money. They wait. They watch your tone of voice. Then, they send a fake invoice from your email to your client. By the time you realize what happened, the money is gone.
Remote Desktop Protocol (RDP): The Hacker’s Favorite Highway
Do your employees log in from home? If your IT provider set up RDP without a VPN or multi-factor authentication (MFA), you might as well leave your server room door open in the middle of a busy street. Hackers use automated scripts to "brute force" these logins 24/7. Once they are in, they have total control over your network.

Why "Good Enough" IT Support Fails Nebraska Businesses
We see it all the time in the Midwest. A business signs a contract with a big-name provider, pays a hefty monthly fee, and assumes they are protected. But when we perform a security audit, we find the "security" is just a basic antivirus and a firewall that hasn't been updated in three years.
Traditional IT support is reactive. They wait for you to call because your printer is jammed. They aren't proactively hunting for vulnerabilities in your infrastructure. At SAINT Technology Services, we take a different approach. We believe in Managed IT Services in Lincoln, Nebraska that are proactive, not just reactive. We close the gaps before the hackers find them.
Ransomware Protection for Small Business: Beyond the Backup
If you think having a backup is enough to stop ransomware, you’re operating on 2010’s logic. Modern ransomware doesn't just encrypt your files; it finds your backups and deletes them first.
Effective ransomware protection for small business requires a multi-layered defense. You need:
- Immutable Backups: Backups that cannot be changed or deleted for a set period.
- Endpoint Detection and Response (EDR): Tools that act like a digital security guard, watching for suspicious behavior in real-time, not just checking for known "bad" files.
- Network Segmentation: Ensuring that if one computer gets hit, the infection can't spread to your entire warehouse or office.
If your current IT provider hasn't talked to you about "lateral movement" or "immutable storage," you don't have a security plan, you have a wish.
Security Awareness Training: Turning Targets into Defenders
You can have the most expensive firewall in the world, but if your receptionist clicks on a link in a "package delivery" email, the firewall won't save you.
This is where security awareness training comes in. Your employees are your largest attack surface, but they can also be your strongest line of defense. We don't just give them a boring 30-minute video once a year. We run simulated phishing attacks to see who clicks. Then, we provide targeted, friendly training to help them spot the red flags.
When your team knows what to look for, your business becomes a much harder target. Hackers are lazy, they’ll move on to a business that doesn't train its people.
Breaking the Licensing Trap: The SAINT Way
One of the biggest "secrets" in the IT world is the overhead of recurring licensing fees. Many vendors will sell you a security system, cameras, door access, etc., and then charge you an annual fee just to keep the software running.
Are you tired of paying for licensing and that annual fee for your security vendor to manage only the cameras and doors? You’re essentially paying a "tax" to use equipment you already bought.
At SAINT, we break businesses free from these licensing barriers. We evaluate your infrastructure and present solutions that eliminate unnecessary overhead. We specialize in setting businesses up with top-tier systems like Ubiquiti. This creates a full ecosystem for your business needs:
- VoIP Phone Systems
- Network Infrastructure
- CCTV/Security Cameras
- Access Control (Keycards and Door Security)
Everything is under one ecosystem with one provider. We’ve seen businesses receive $20k quotes for access control systems that come with massive annual fees. We’ve turned those into practical, high-performance solutions for a fraction of the cost.
For example, we recently helped a health and wellness business that wanted 24/7 customer access. The quotes they received were so high that the annual fees would have killed their profit margins. We stepped in, offered a full ecosystem, and broke them away from those fees. Now, the only time they pay is when they need a change outside their control. We even empower businesses who want to self-manage by setting them up the right way and handing over the keys.
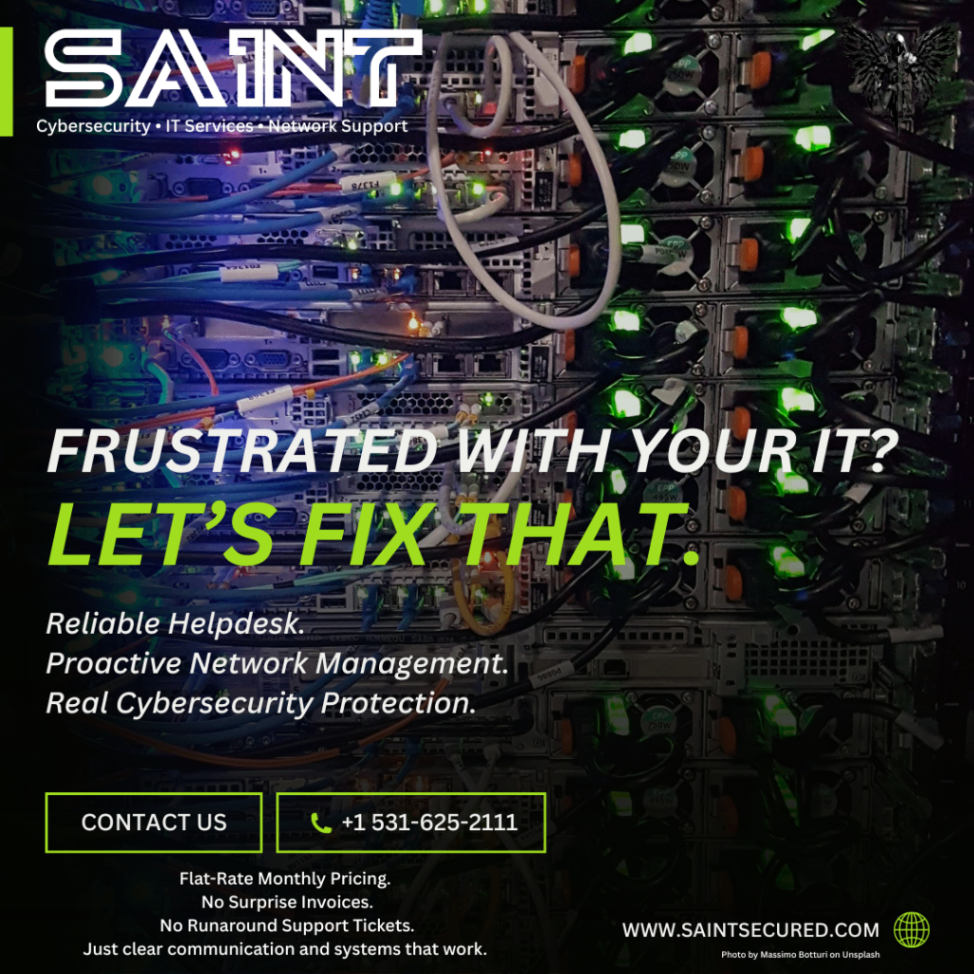
How SAINT Technology Services Protects Your Business
We aren’t your typical IT company. We are veteran-owned and Midwest-rooted. We bring military discipline to your technology infrastructure. When we take on a new partner in Omaha or Lincoln, we don't just "maintain" your systems, we stabilize and optimize them.
We look at your entire technology ecosystem to see where we can save you overhead. Whether it's consolidating your cloud subscriptions or replacing an overpriced security vendor, our goal is to make your business more profitable and more secure.
If you’re looking to break free from high-priced recurring licensing fees and want a partner who actually understands the threats facing Nebraska businesses, we’re ready to talk. We provide the convergence of physical security and cybersecurity that modern businesses need to thrive.
FAQ: Cybersecurity for Nebraska Small Businesses
1. Why is my business a target if I don't have "valuable" data?
Hackers don't just want data; they want your computing power, your bank account access, and your reputation. They can use your business as a "jump point" to attack larger companies or lock your files until you pay a ransom. To them, it’s a volume game.
2. Is "The Cloud" safer than an on-site server?
Generally, yes, but only if configured correctly. Cloud providers like Microsoft and Google secure the infrastructure, but you are responsible for securing your data and your users. Without MFA and proper permissions, the cloud is just someone else's computer that you've left unlocked.
3. What is the most important security step I can take today?
Turn on Multi-Factor Authentication (MFA) on every single account that allows it, especially your email and your Physical Security in Gretna, NE management portals. It stops over 90% of automated attacks.
4. How often should we do security awareness training?
Security should be a continuous conversation, not an annual event. Monthly micro-training and regular phishing simulations are the most effective ways to keep security top-of-mind for your staff.
5. Can I really eliminate annual licensing fees for my cameras and door locks?
Yes. By using ecosystems like Ubiquiti, you own the hardware and the software. There are no "per-camera" or "per-door" monthly fees. You get professional-grade security without the "vendor tax."
6. Does SAINT support Apple, Windows, and Linux?
Yes. We have the expertise to manage mixed environments. Whether your office runs on Macs or your warehouse runs on specialized Linux systems, we can secure and manage it all.
7. How do I know if my IT provider is actually doing their job?
Ask for a security audit or a report on your patch status and backup health. If they can’t give you clear, transparent data on your network's health within 24 hours, they probably aren't being proactive.
8. What should I do if I think I've been hacked?
Disconnect the affected device from the internet immediately, but do NOT turn it off. Turning it off can erase volatile memory that helps IT experts trace the attack. Call a professional security partner like SAINT immediately.
Related Services:
- Managed IT Services
- Cybersecurity & Threat Mitigation
- Ubiquiti Network & CCTV Deployment
- VoIP Business Phone Systems
- Access Control Solutions
Serving Businesses in Nebraska:
- Lincoln
- Omaha
- Gretna
- Bellevue
- Fremont
- Grand Island
If your business in Lincoln or Omaha is dealing with slow systems, downtime, or unreliable IT support ( SAINT fixes it before it becomes a problem.)



